The past week saw a number of breaches of usernames and passwords from well-known websites. People are prone to reuse passwords across personal and corporate accounts, and compromised social networking accounts can be used to conduct social engineering attacks.
These incidents have the potential to impact on your own organisation but it can be difficult to prioritize them alongside other incidents. For a large organisation with many thousands of users the process of notifying and supporting affected individuals can be involved and time consuming.
What should you take into account when determining the urgency of your response to these events?
A number of factors are the same for everyone affected by the breach. These are things under the control of the breached party rather than the user or your own organisation. Two key things to consider are how the breached party responds to the incident and the level of protection that they had given to the compromised passwords.
The response of an organisation to a breach ranges from nothing (perhaps they are in denial, or they have ceased to operate) to a proactive response that preempts any public release of data. Risks will vary according to the level of protection afforded to the passwords – from plain text to salted hashes that are intensive to crack (you should also take into account the resources available to your adversary).
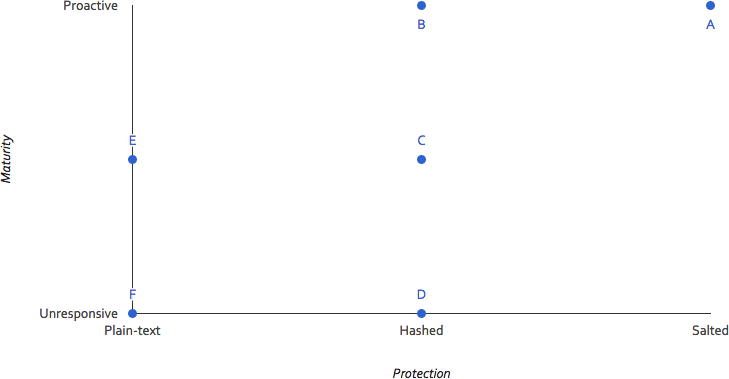
These two factors are also likely to have a large impact on the advice and support you want to issue to your users. If the organisation responded quickly to notify and support its users, there is likely little that you can add.
Other factors are dependent upon your own organisation and users. How many of your users are affected by the breach? Are you able to identify them (https://haveibeenpwned.com/ is an excellent source of data for individuals and organisations)? Do they still work in your organisation? Did they use a unique password, or reuse their corporate password? How old is the breach in comparison to the age of your user accounts and password policies (CESG recommend that passwords should not routinely expire)?
Your incident response process needs to be aware that incidents that happen to others. It needs to take into account the types of information above to help you assess the impact of the incident and prioritize limited information security efforts.
